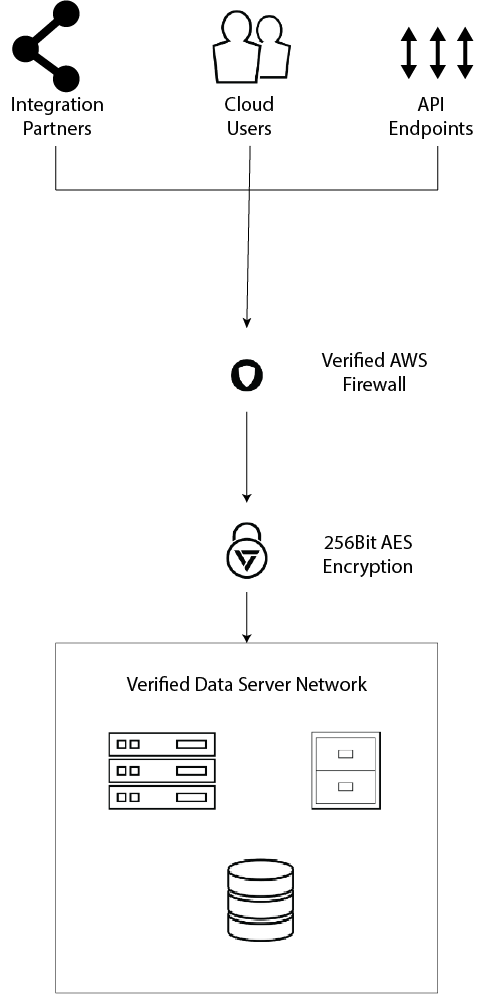
Securing your data at capture, transmission and rest
Verified takes pride in securing your data and transactions from the point of capture through to our secure storage solutions - protecting you and your customer every step of the way.
Our security protocols use the latest encryption and privacy tools to ensure your data remains private and can only be accessed by authen ticated processes. All of our platforms use a minimum of:
- Secure connection to web platform using 256bit AES encryption for the symmetric key and 4096 bit encryption for the certificate.
- Obfuscated file and directory structure to reduce likelihood of connecting images with their associated context data
- HIPAA compliant and secure data centers in low-earthquake risk zone <
- Password and user data encrypted using NSA designed one-way cryptographic SHA functions (512bit)
- Full security and access logging
- Role and Permissions-based access