End to end Encryption
Capture | Transmission | At Rest
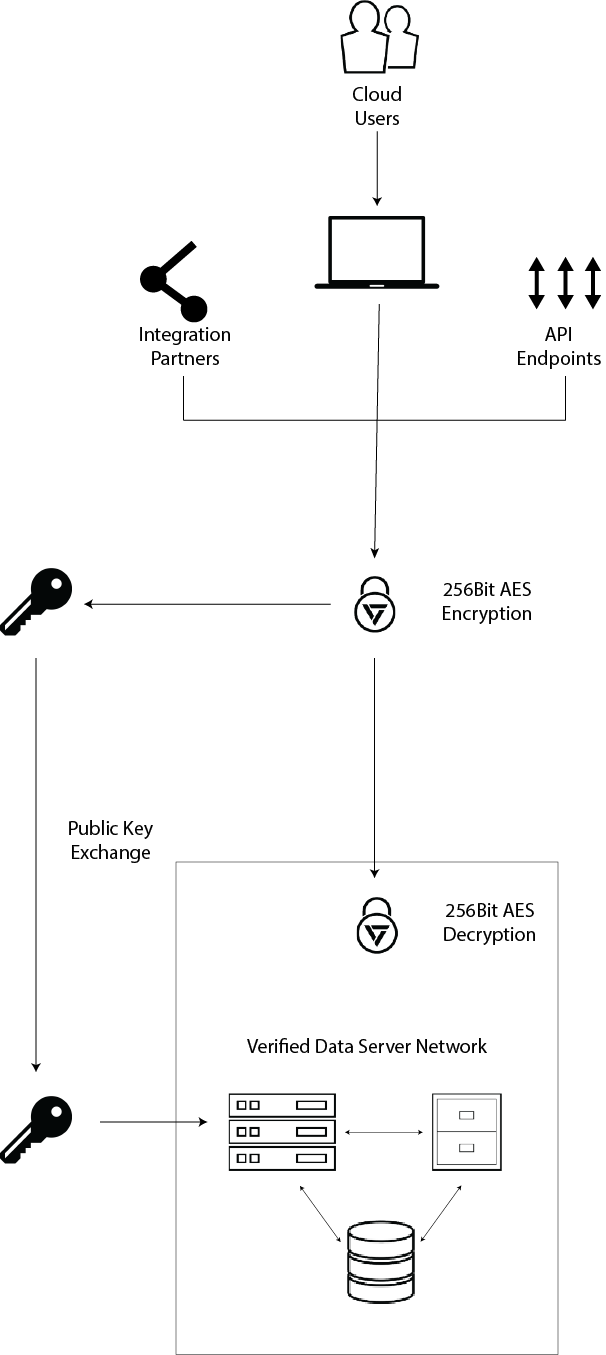
Verified products benefit from complete end-to-end encryption of all documents and data from the point of capture, through transmission and when at rest in our secure storage servers. Encrypted data simply changes the format of the data using an encryption key and algorythms that change the data from its raw form into a jumble of letters, numbers and special characters that make no sense without the opposing decryption key.
Encryption methodsUsing the latest enterprise-grade encryption methods, Verified takes the data you collect through the platforms, encodes it with 256Bit Encryption and transmits the encrypted data through a secure socket layer (SSL) to our data servers.
Using private keysThe Verified platforms gain acces to our server network using a sequence of secure public and private keys. with synchronised key sharing, the server network will only accept data from authenticated sources, adding another layer of security to your data throughout its lifecycle.
Decrypting your dataAs your data is received we reverse the process and decrypt it using 256 Bit decryption methods. Our algorthyms reverse the process we use to encrypt your data ready for processing or long term storage.
Neatly wrapped up with secure hostingIf the privacy and encryption controls we offer just aren't enough, you can be confident that our server infrastructure is also robust, offering secure hosting behind network load balancers and a private firewall. Find out more about our hosting here.